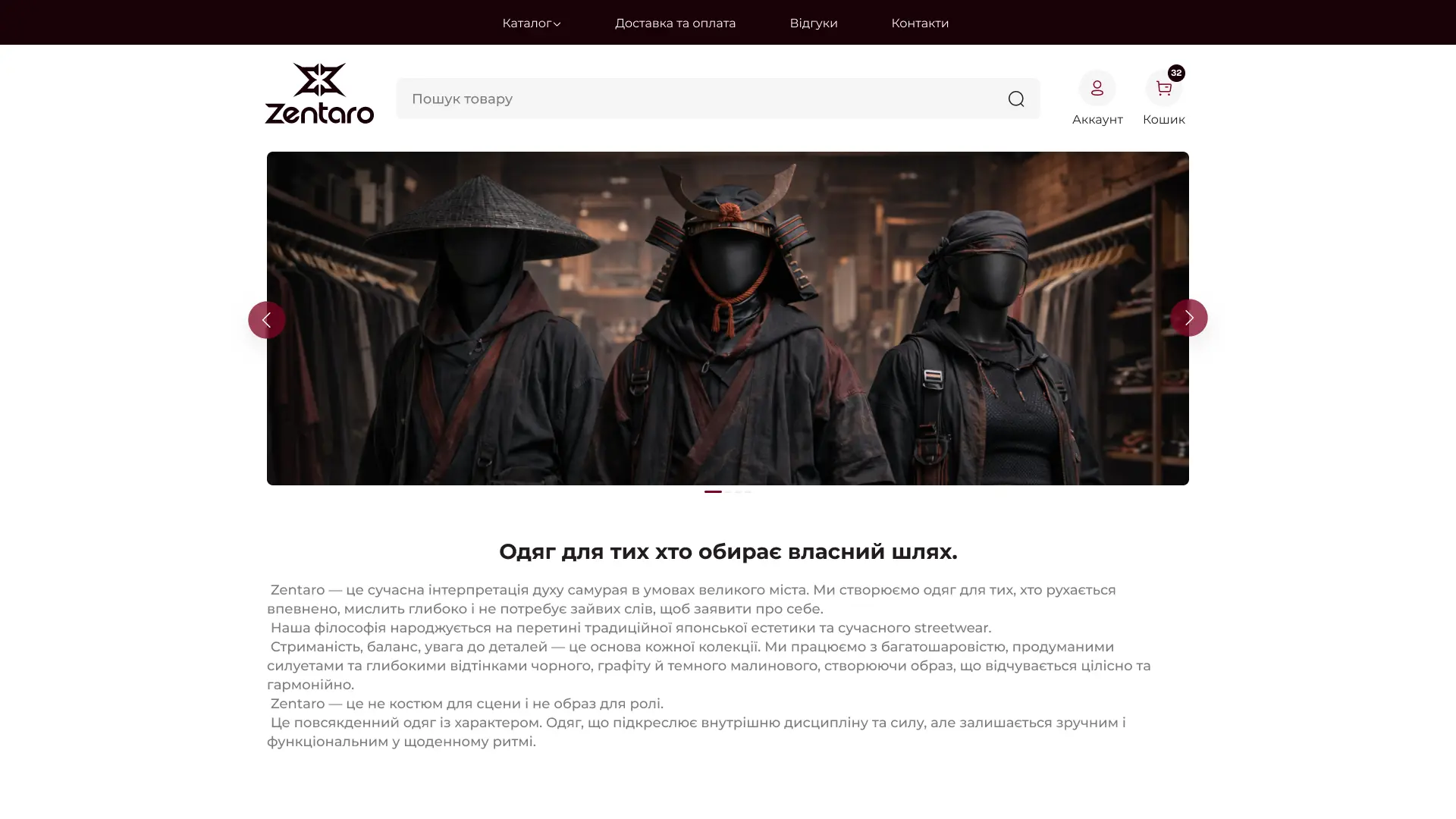
We have formed a catalog structure with thoughtful filters, separate collections, and quick transition to purchase.
The Zentaro philosophy was conveyed through deep dark shades, contrasting typography, and an emphasis on fabric details.
We implemented management of products, sizes, balances, and orders with a flexible admin panel.
We created a logical catalog structure with multi-level filters by equipment type, power, brand, and purpose.
Visually, technical reliability and a professional approach were emphasized through a restrained color scheme and clear typography.
We implemented flexible management of products, characteristics, filters, and integration with CRM to automate applications.
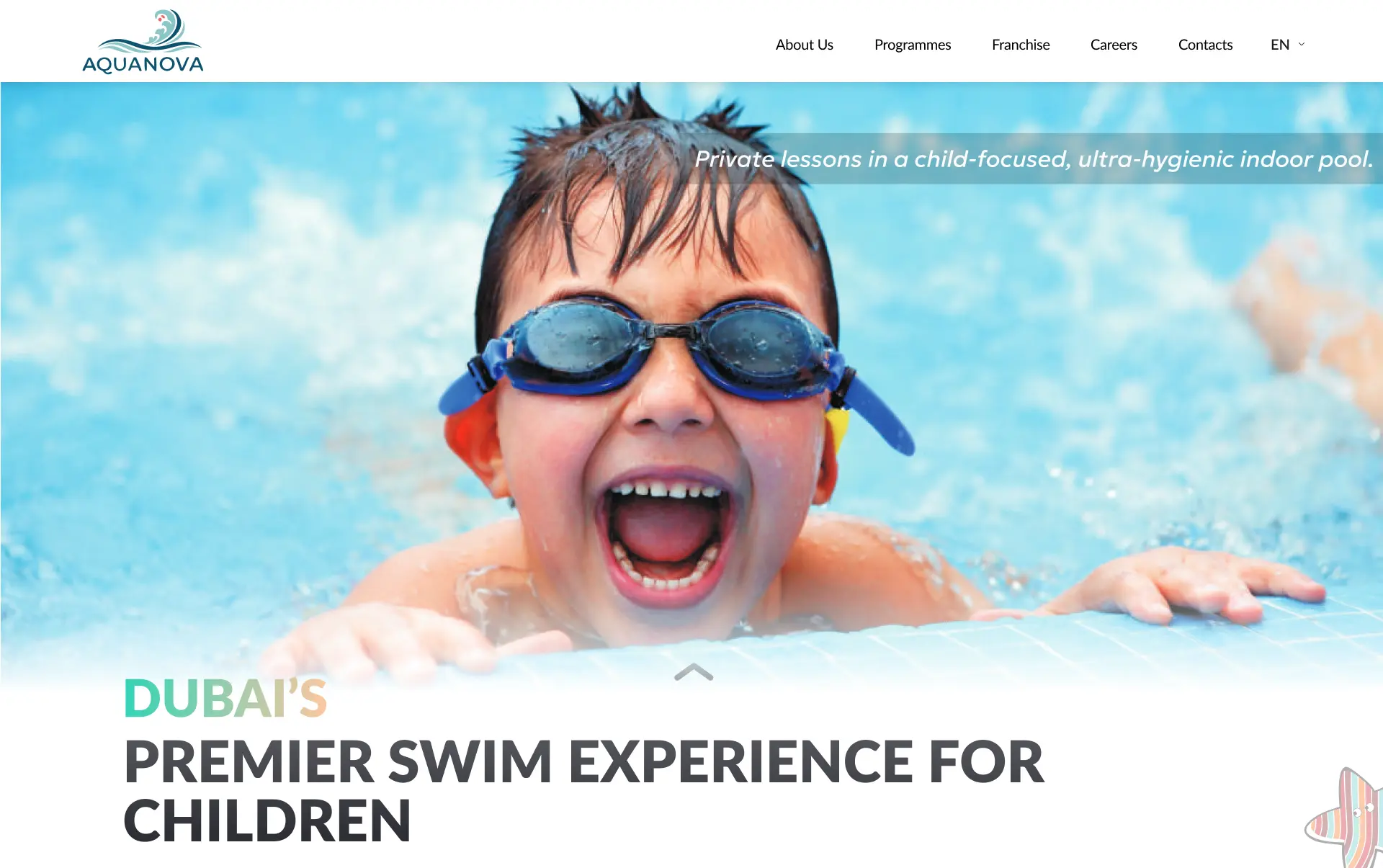
We built a structure that logically leads from benefits to registration. We emphasized privacy, water safety, and the coach's individual approach.
Clients gained access to class history, subscription management, and online payments.
We automated the schedule, pool loading control, and communication with parents.
We conduct a deep analysis of the code, server, CMS, and plugins for known vulnerabilities. We check for suspicious files and activity.
Based on the audit, we form a clear action plan: which vulnerabilities to close first, how to configure CMS updates, and what site protection protocols to implement.
We configure firewalls (WAF), DDoS protection systems, and strengthen server configuration. We guarantee that your e-commerce will be resistant to external threats.
We are implementing an automatic system for regular backups (Daily/Weekly) of all files and databases to remote and secure servers.
We implement systems that monitor any suspicious activity, hacking attempts, or changes to site files 24/7. If anomalies are detected, the system instantly sends notifications.
We train your team on cyber hygiene rules (complex passwords, be careful with links). We provide ongoing technical support for rapid response to incidents.
Imagine that your online store is already growing. Orders are coming in steadily and in large volumes, and you can no longer manage inventory storage, pack each parcel, and run to the post office yourself. Managers spend hours on logistics instead of sales. If you constantly think, “Where can I get more warehouse space?”, it’s […]
B2B e-commerce is the stage of a company’s maturity when direct business-to-business sales exceed retail in volume. If you still manage wholesale clients through email, Excel spreadsheets, and phone calls, you are not controlling your business potential. Instead, you depend on the human factor. Creating a B2B portal is not an expense for a new […]
If you don’t measure, you don’t manage. An online store owner who makes decisions based on intuition is like a driver with their eyes blindfolded. Today, Google Analytics 4 (GA4) is not just a trendy tool — it is a critically important instrument for the survival and growth of your business. We will show how […]
Security and Updates: the invisible perimeter of your online store’s profitability
Have you ever considered how much an hour of downtime of your e-commerce costs during peak season? And how much will the loss of your customer database cost due to a data breach? In a world where cyber threats evolve faster than Google algorithms, online store security is not just an IT checklist item.
It is an invisible but rock-solid perimeter of your reputation, stability, and ultimately, profit. Outdated software is not old furniture—it is an open door for attackers.
At Kliox, we build not just protection, but a proactive, layered defense that ensures peace of mind and uninterrupted operation of your digital asset.
When stability turns into vulnerability: the cost of delayed updates
Entrepreneurs often postpone updates to CMS or plugins, fearing they might break the site. However, this stability is illusory and creates far greater risks than the temporary inconvenience of updating. Here are the main ones.
Vulnerability windows that lead to losses
Every software vendor (CMS, plugins, themes) regularly releases patches. These patches primarily fix vulnerabilities discovered by attackers. By ignoring these updates, you are knowingly leaving your online store exposed. It is like patching a hole in the roof during rain with a sheet of paper.
Hidden penalties and reputational damage
A website breach is not only direct financial losses from downtime. It also involves leakage of customers’ personal data (emails, phone numbers, addresses), which can result in multimillion fines under GDPR (for European customers) or Ukrainian data protection laws.
Moreover, it destroys trust. Imagine the cost of rebuilding your brand if news of a breach spreads.
Layers of protection: a security architecture that does not fail
We build website protection based on the principle of layered defense, where each element reinforces the others. What do we prioritize?
Security perimeter: your cyber border
Our first step is infrastructure configuration. This includes web application firewalls (WAF), DDoS protection systems, and server hardening. This is the first line of defense that blocks up to 90% of threats before they reach your e-commerce.
Code and components: the core of reliability
Code integrity — we regularly audit both our own code and all third-party modules for vulnerabilities.
Regular updates — we ensure timely updates of CMS, plugins, and themes, which is basic hygiene for maintaining stability and protection.
SSL certificate: the invisible trust protocol
HTTPS with an SSL certificate is not just a green padlock. It is a cryptographic shield that encrypts customer data (payment and personal) during transmission.
For an online store that processes financial transactions, this is an absolute standard. The absence of SSL is a direct signal for browsers to mark your site as unsafe, instantly deterring customers.
Security lifecycle: from monitoring to rapid recovery
Security is not a set-and-forget task. It is a continuous process.
- 24/7 anomaly monitoring
Our systems continuously track any suspicious activity: unusual login attempts, changes in site files, abnormal traffic. When a threat is detected, the system immediately sends alerts.
- Backups: your digital insurance policy
Even the strongest defense can be breached. That is why we implement automatic, multi-level backups (files and databases) to remote and secure servers. In case of a breach, failure, or data loss, we can restore your online store to working condition within hours, minimizing downtime and financial losses.
- Staff training: the human factor under control
The weakest link in any security system is the human factor. We conduct training for your employees on cybersecurity hygiene (secure passwords, phishing, working with the admin panel).
Security ROI: how protection turns into predictable profit
Investing in e-commerce security means investing in your peace of mind, reputation, and stable sales flow. This process is based on three pillars.
Profit protection — every hour of downtime due to an attack costs you lost orders. Our stability ensures your business is available 24/7.
Trust building — customers choose reliable stores. SSL, data protection, and proactive incident response build a reputation that attracts new buyers.
Cost savings on damage recovery — the cost of restoring a site after a breach and mitigating consequences can be dozens of times higher than the cost of preventive website protection.
Conclusion on online store security and updates
Security and online store updates are not a technical burden, but a strategic investment in the long-term stability and profitability of your business. At Kliox, we create this invisible yet reliable defense.
Does your online store need reliable protection? Order a free security audit from Kliox. We will conduct a deep analysis of your site, identify critical vulnerabilities, and develop a tailored e-commerce protection plan that ensures your peace of mind.